Security Assessment
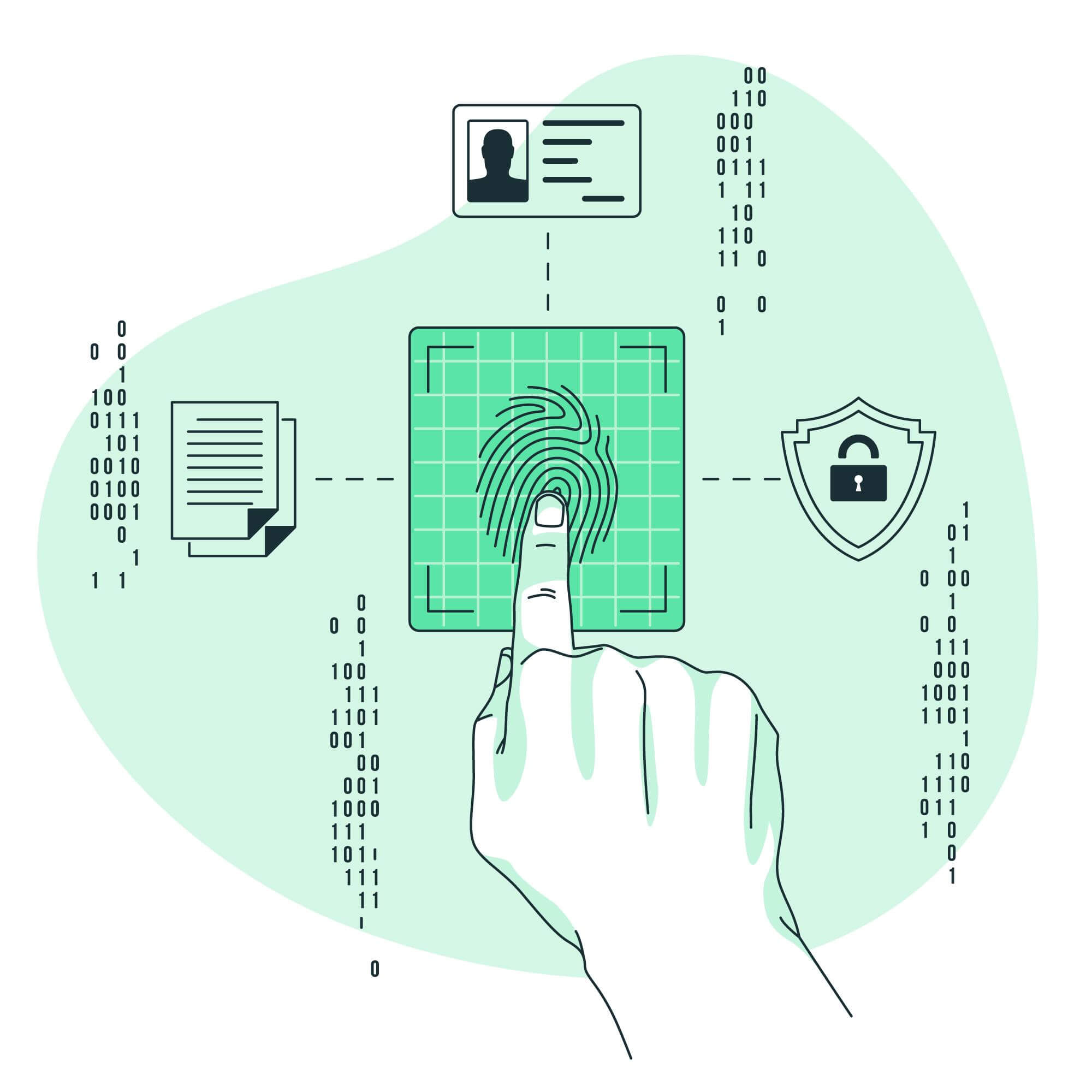
Bridge the Gap to Simpler Security
Identify loopholes and ensure your business is safe from threats outside and inside
Our Security assessment aka Petests methodically test the security of your IT infrastructure, your employees, data, applications and other assets using sophisticated real-world attack patterns to uncover risks and provide fix solutions. Unlike a malicious hack, penetration testing is performed by experts legally against a predefined scope at an arranged time.
Our Assessment Approach
Test your security against real-world attacks,
Without the risks of negative headlines
Without the risks of negative headlines
What You Will Receive

Professional and comprehensive

Real time communication and collaboration.

Fixes and Solutions for found flaws.
Expert support and assistance.















 info@sentryark.com
info@sentryark.com